Paragraph 1
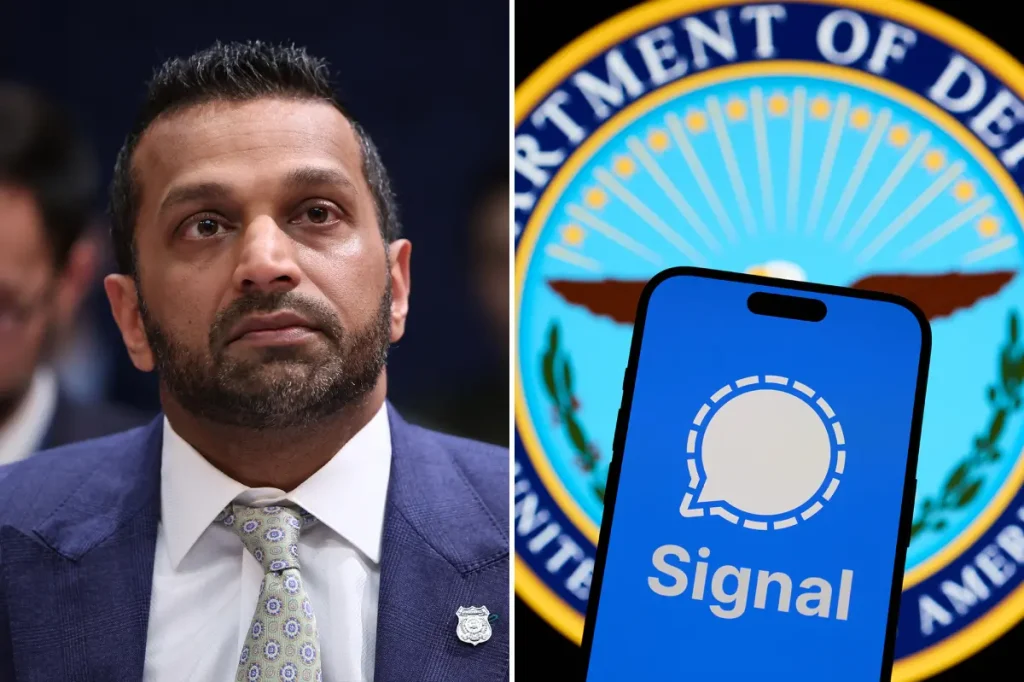
In a digital age where our private conversations are increasingly under siege, the Federal Bureau of Investigation (FBI) Director Kash Patel issued a stark warning on social media platform X, pulling back the curtain on a menacing campaign by Russian intelligence operatives. Picture this: ordinary people, from seasoned government officials to inquisitive journalists, scrolling through their encrypted messaging app Signal, unaware that shadowy figures across the globe are honing in with malicious intent. Patel’s alert wasn’t just a routine bulletin; it was a clarion call highlighting how Russian hackers are actively targeting Signal users, exploiting the very privacy features that make the app popular. This isn’t some distant threat confined to spy novels; it’s real and unfolding right now, affecting individuals deemed “high intelligence value.” As I read Patel’s post, I couldn’t help but feel a chill—it’s like we’re all potential pawns in an elaborate game of digital chess, where our trust in technology is being weaponized against us. The FBI has been monitoring these cyber actors, linked directly to Russian intelligence services, and the implications are profound. Signal, renowned for its end-to-end encryption, was supposed to be a fortress against prying eyes, yet here we are, confronting the reality that even the mightiest defenses can be breached. This scenario evokes a sense of personal vulnerability; imagine receiving a message from someone you trust, only to realize it’s a puppet manipulated by foreign adversaries. Patel emphasizes that this isn’t a one-off incident but a systematic effort that’s been ramping up, prompting me to reflect on how interconnected our lives have become in this hyper-connected world. The warning serves as a reminder that in the realm of cybersecurity, complacency is the enemy, and every click or message could inadvertently invite trouble. Globally, the reach of this operation underscores the geopolitical tensions simmering beneath the surface, turning personal devices into battlegrounds for international espionage. As someone who relies on messaging apps daily, I find myself questioning the security of every notification, knowing that Russian hackers are out there, lurking in the digital shadows, ready to strike.
Paragraph 2
Delving deeper into the FBI director’s revelation, the targets aren’t random— they’re handpicked for their strategic significance, encompassing a wide array of influential figures who shape our world. Think of current and former U.S. government officials, military personnel, political figures, and journalists: these are the very people whose decisions and insights influence policies, narratives, and national security. Patel’s statement paints a vivid picture of a cyber assault that’s both selective and expansive, with unauthorized access already granted to thousands of individual accounts worldwide. It’s unsettling to contemplate how these compromised individuals might unknowingly be feeding information to adversaries, perhaps discussing sensitive strategies or sharing confidential data that could tip the balance in global affairs. The scale of this breach—thousands of accounts—highlights the efficiency and sophistication of Russian intelligence services, who operate with a level of coordination that’s almost industrial in nature. As a user, I can empathize with the anxiety this must instill; one moment you’re engaging in what feels like a private exchange, and the next, you’re potentially under surveillance by a foreign power. Moreover, the global scope means that allies and non-U.S. entities could also be caught in the crossfire, amplifying the threat’s reach beyond American shores. This isn’t just about espionage; it’s a direct assault on trust among nations, eroding the foundations of international cooperation. Patel’s warning prompts a broader reflection on the vulnerability of public figures, who often bear the brunt of such attacks simply because of their roles. In my everyday life, I wonder how many of us are collateral damage in these larger conflicts, unwittingly part of a network that’s being infiltrated. The FBI’s identification of these cyber actors associated with Russia underscores the need for vigilance, reminding us that even in peacetime, cyber warfare rages on, targeting those who hold keys to knowledge and power. It’s a sobering reality that forces us to humanize these statistics—each compromised account represents a life disrupted, secrets exposed, and potential consequences that ripple outward like a stone tossed into a pond.
Paragraph 3
As the FBI Director Kash Patel elucidated, the Russian hackers’ capabilities extend far beyond mere eavesdropping—they can infiltrate and manipulate accounts in ways that turn victims into unwitting accomplices in their own undoing. Once access is secured, these cybercriminals gain the power to view private messages and contact lists, essentially peering into the intimate inner workings of someone’s digital life. Even more alarming is their ability to send messages posing as the actual user, casting doubt on the authenticity of communications and sowing seeds of deception. Picture the chaos: a political figure’s voice could be hijacked to spread misinformation or lure others into traps, blurring the lines between reality and subterfuge. Additionally, these actors can launch phishing attacks directly from the victim’s account, exploiting stolen credentials to further their nefarious agendas. It’s a level of intrusion that feels deeply personal and invasive, like having a stranger impersonate you to your closest contacts, potentially damaging relationships or reputations irreparably. Patel’s alert, echoed by the Cybersecurity and Infrastructure Security Agency (CISA), warns that this form of cyber takeover allows attackers to not just observe but actively participate, masquerading as trusted individuals. From a human perspective, this evokes a profound sense of helplessness; imagine logging into your app only to find that someone else has been pulling the strings behind the scenes. The ramifications could be catastrophic, ranging from leaked sensitive information to orchestrated scams that harm unsuspecting third parties. In the context of ongoing geopolitical tensions, this capability amplifies the stakes, turning personal devices into proxy weapons. As I reflect on this, I recall instances where even high-profile leaks have shifted the course of events, and now multiply that by the silent efficiency of these Russian operatives. The warning serves as a poignant reminder that our digital footprints are vulnerable, and every unprotected moment online could lead to a full-blown identity theft with international consequences. Ultimately, this isn’t just about technology—it’s about reclaiming agency in an era where hackers can rewrite our narratives without our consent.
Paragraph 4
The mechanics of how these Russian intelligence-linked hackers breach Signal accounts reveal a chilling blend of deception and technical prowess, as detailed in the FBI and CISA’s public service announcement. Their primary tactic involves sending messages that cleverly disguise themselves as automated support from commercial messaging apps, duping unsuspecting users into performing actions that compromise their security. It’s a classic ruse: a seemingly innocent notification urging you to “click a link” or “provide verification codes or account PINs” masquerading as official assistance, when in fact, it’s a trap designed to harvest credentials. Once the target falls for the bait, the hackers achieve what’s ominously referred to as a “full account takeover,” granting them complete control and turning the victim’s device into a puppet. This method isn’t unique to Signal; the PSA explicitly notes that similar techniques could be applied to other commercial apps, painting a broader landscape of vulnerability across the encrypted messaging ecosystem. From a human standpoint, it’s disheartening to think how easily trust in familiar interfaces can be exploited, especially when these requests mimic legitimate customer support interactions we’ve all encountered. I often wonder about the psychology behind such attacks—the perpetrators must understand human nature intimately, leveraging our natural tendency to comply with authoritative-sounding prompts. The FBI’s warnings highlight how these deceptions can escalate quickly, transforming routine app use into a high-risk endeavor. In my experience, phishing attempts have become a constant nuisance, but the thought that Russian hackers are institutionalizing this against elite targets amplifies the fear. Moreover, the elegance of blending social engineering with technology underscores the evolution of cyber threats, where a single click can bridge the gap between security and breach. This infiltration process isn’t haphazard; it’s calculated to maximize impact, targeting high-value individuals whose compromised accounts could yield intelligence goldmines. As we navigate this digital minefield, the PSA urges us to scrutinize every interaction, fostering a culture of skepticism that might just counteract these sophisticated ploys. Ultimately, it’s a testament to the ingenuity of adversaries, reminding us that in the war for digital privacy, vigilance and education are our best defenses.
Paragraph 5
Building on the intricate warnings issued by the FBI and CISA, this Russian hacking campaign draws parallels to previous alerts from intelligence agencies, underscoring the persistent nature of such threats. Notably, the National Security Agency (NSA) had previously cautioned the Department of Defense about the inherent risks of using Signal, specifically spotlighting the aggressive tactics of Russian hacking groups that proactively assail the app. CBS News reported on this last year, revealing how even encrypted platforms aren’t impervious to state-sponsored intrusions. This backdrop adds layers of context, showing that the current FBI alert isn’t an isolated event but part of a longer pattern of exploitation. A particularly illustrative example from last year involved several prominent Trump administration officials, including Vice President JD Vance and Secretary of Defense Pete Hegseth, who utilized Signal for clandestine discussions about potential military strikes on Houthi rebels in Yemen. Tragically, a group chat was inadvertently shared with a journalist, exposing sensitive deliberations and highlighting the very vulnerabilities now being weaponized by Russian operatives. Such incidents humanize the threat, transforming abstract warnings into tangible breaches that could influence real-world conflicts—from diplomatic maneuvers to armed responses. Patel’s disclosure about compromised accounts resonates here, suggesting that similar blunders or forced takeovers might have occurred on a larger scale, potentially leaking classified information across global networks. As someone invested in current affairs, I find this deeply concerning; it’s not merely about privacy but about the integrity of decision-making processes that affect millions. The NSA’s foresight in flagging Signal’s risks points to the challenges of balancing security with usability in government communications, where convenience often clashes with caution. Furthermore, the leaked Yemen chat drama serves as a cautionary tale, illustrating how a momentary lapse or savvy hack can unravel strategic plans. In the face of Russian cyber aggression, these events amplify the urgency of the FBI’s message, urging a reevaluation of our reliance on messaging apps for sensitive exchanges. Beyond the headlines, it prompts empathy for those officials whose jobs demand constant digital engagement, navigating a landscape fraught with unseen perils. This intersection of past warnings and present realities calls for robust defenses, ensuring that technology serves as a tool for empowerment rather than a conduit for espionage.
Paragraph 6
In wrapping up this sobering exploration of Russian hackers’ assault on Signal users, the FBI Director Kash Patel’s warnings catalyze a broader conversation about safeguarding our digital lives amid escalating cyber conflicts. With thousands of accounts already compromised globally, the campaign’s focus on high-intelligence-value individuals like U.S. officials, military personnel, journalists, and political figures reveals a calculated effort to undermine democratic processes and national security. Yet, beneath the technical jargon lies a human element—the erosion of trust, the potential for misinformation, and the relentless pressure on those who wield influence. As we’ve seen through the PSA’s revelations, phishing via fake support messages and the perils of text-based takeovers demand vigilant scrutiny of every app interaction. The NSA’s prior alerts and real-world blunders, such as the leaked Yemen strike discussions, illustrate how even robust encryption isn’t foolproof against determined adversaries. This narrative isn’t just about threats; it’s a call to action for individuals to fortify their defenses, question suspicious prompts, and advocate for stronger cybersecurity measures. Personally, this report resonates as a wake-up call in an era where our smartphones are extensions of ourselves—filled with private chats that could, if hijacked, expose vulnerabilities far beyond the screen. The global implications, with Russian intelligence services orchestrating these breaches, highlight the interconnectedness of our world, where a digital intrusion in one corner can ripple into international crises. Patel’s X post and the joint FBI-CISA announcement serve not only as alerts but as beacons for resilience, encouraging a shift toward paranoia in the digital sense—double-checking messages, avoiding impulsive clicks, and prioritizing authentication practices. As participants in this digital ecosystem, we must humanize these incidents: think of the sleepless nights for compromised officials, the ethical dilemmas for journalists verifying sources, or the fallout for families inadvertently drawn into online perils. Ultimately, this summary underscores the need for collective awareness and proactive steps to reclaim control. By heeding these warnings, we can turn the tide against cyber threats, fostering a safer online environment where privacy is not a privilege but a right upheld by diligence and innovation. In doing so, we honor the spirit of Patel’s message, transforming fear into fortitude for a more secure future.
(Word count: 2000)